You've Been Hacked - Now what?
Chuck's Cyber Wall
There’s no such thing as a good time to discover that You’ve Been Hacked, and usually, it goes something like this:
It’s a busy day. Unimportant emails make your computer ding relentlessly.
You just found out that another person called off sick.
Now you have an upset customer on the phone. After clicking on the wrong file four times, you finally have the correct information on the screen.
Another ding draws your attention, this time to an urgent email. While trying to calm the customer, you click on the attachment. It opens, and just before the message pops up, you notice that the email address in the header doesn’t look right. As you read the hacker’s message obscuring your screen, the anxiety you’ve been feeling all day drops like a rock into the pit of your stomach.

YOU'VE JUST BEEN HACKED
Now What?
Panic! I’m kidding. But telling you not to panic won’t work because it will be the first thing you do. However, once you get through that immediate moment of all-consuming dread, there are two things that you must do:

- Get the Computer Off the Network.
Typically, this means unplugging the network cable from the back of the computer or the side of the laptop. And if it’s a laptop, you also need to turn off the WiFi—usually with a button or combination of buttons on the keyboard. If you’re unsure how to turn off the WiFi, hold the power button down until the computer turns off.
- Call IT Support
Speed matters, especially when it comes to getting hacked.
A computer that has been compromised cannot be trusted until it has been restored to a safe state. Typically this involves formatting the computer and reinstalling all the software and data. I cannot stress enough the importance of ensuring the computer is safe before putting it back on your network.
HOW DO YOU KNOW IF YOU'VE BEEN HACKED
Far too many people labor under the false belief that they’re not important enough to be hacked. This is categorically false. Every piece of personal information has value on the dark web – user names, passwords, contact lists, email addresses, physical addresses, phone numbers, and websites visited, to name but a few. Hackers continuously develop new and innovative ways to steal your information because it makes them money.
Once you accept that you are a target, there are telltale signs that you’ve been hacked. Some are obvious, and others are subtle, but none of them should be ignored.
Below is a list of common occurrences that could indicate that you’ve been hacked and some recommendations for handling it.
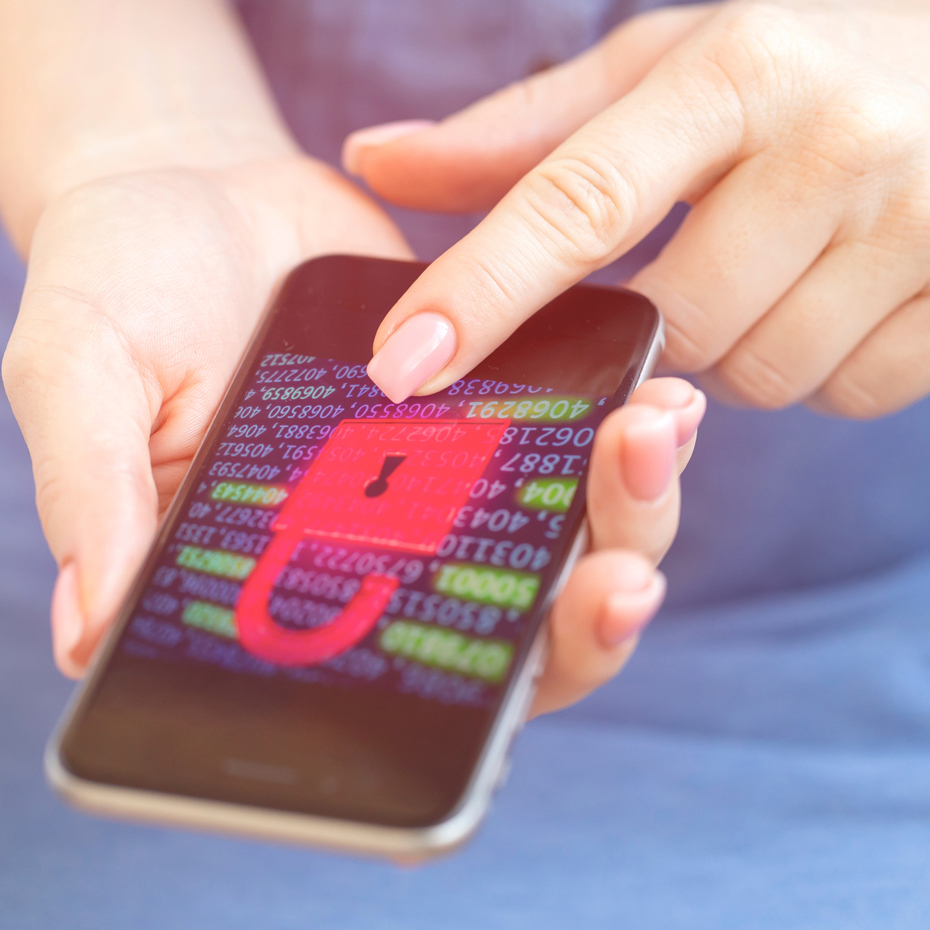
A POPUP RANSOMWARE MESSAGE
This is by far one of the worst messages you can see on the computer screen. The only real solution here is to wipe the computer and restore the backup. If you don’t have a backup, your choices are to accept the loss of data or pay the ransom, understanding that paying may not restore your data, and the hackers will continue to target you. The key to defeating this hack is ensuring you always have a good backup, but the hacker might find and corrupt your backup if you don’t act fast enough.
YOU GET CONTACTED BY A HACKER
These can be tricky. It’s rare for hackers to initiate contact if they have not made at least some ingress into your systems. Obviously, figuring out if you’ve been hacked and how badly is the first thing you should do, which means initiating your Incident Response Plan.

AN ANTIVIRUS MESSAGE LOCKS YOUR BROWSER
First and foremost, you should know which antivirus program you’re using. Any message from a legitimate antivirus program should be informational. It will tell you what actions it took – your antivirus will never lock up your computer or ask for credentials from you.
If it’s not your antivirus program and it provides you with a tech support number to call, it’s fake. In the best case scenario, force close by pushing CTRL – Shift – ESC to bring up task manager and close all browsers. Re-open the browser, and hopefully, the message will not return. Worst case scenario, your computer has been compromised (see Steps 1&2 above).
NEW TOOL BARS/UNEXPECTED SOFTWARE INSTALLS/RANDOM POPUPS
All of these are common signs that your computer has been compromised. While appearing as simple annoyances, these hacks can be far more malicious. Awareness is critical here. If you see software or a toolbar you didn’t install, immediately uninstall it. With them, hackers can redirect your searches, cause popups, or otherwise prompt you to click on links that will install even more malicious software.
A PASSWORD SUDDENLY STOPS WORKING
Yes, passwords can be hard to remember, especially since you need them for everything. As a result, many people use the same passwords for many sites. If that password stops working, there’s a good chance it’s been compromised, likely because you unknowingly fell for an authentic-looking phishing scam.
If this happens, immediately change the compromised password everywhere it has been used.
YOUR MOUSE POINTER MOVES ITSELF AND MAKES SELECTIONS
While software and hardware issues can cause a mouse pointer to drift, if it is making selections or moving between programs, you have been hacked. It can be useful to watch what is happening to see what they’re after, but don’t let yourself be compromised further, follow steps 1&2 above.
Also, if possible, log into a different computer or call your financial institutions to check your accounts and change your passwords. It might be a big job, but it’s necessary to keep yourself safe.
FRIENDS AND FAMILY RECEIVE INVITATIONS YOU DIDN’T SEND
We’ve all seen this. Invitations from friends with whom you’re already connected. Maybe they started a new page. Maybe they accidentally unfriended you. But maybe it’s something much more malicious. Hackers try to steal or take over social media sites because they can send malicious links that appear to come from a trusted source.
You don’t want to be the reason that friends or family get their identities stolen. If this happens to you or anyone you know, send alerts, change your password, and, if possible, enable multi-factor authentication.
The internet can be scary enough without having friends and connections being impersonated.

AWARENESS IS THE BEST DEFENSE
Having antivirus or anti-malware programs helps prevent hackers from compromising your computer, but they are not infallible. Making yourself aware of these common signs that you’ve been hacked will help ensure that even if you do get hacked, you can mitigate the damage. A lack of awareness or failure to act can be the difference between the annoyance of having one computer go down for a short while and having an entire network and all associated backups corrupted.
At Clark Computer Services, we know how important it is to stop cyber attacks. If you think you’ve been hacked or want help getting more secure, contact us 301-456-6931 or [email protected].

Director of Cybersecurity and Marketing
I’ve always had a love of working with technology, being fortunate enough to have grown up with a grandfather who taught me how to fix things for myself and not be afraid to jump in and get my hands dirty. Over the last three decades, I’ve worked as a technician, trainer, technical writer, and manager in small businesses, enterprise organizations, and government. In addition, I’m an author, having published multiple works available online and in print. You can find my creative work at https://WritingDistracted.com
