Why Are There So Many Cyberattacks?
Chuck's Cyber Wall
With so many Cyberattacks prevalent today, we rarely discuss them as a whole – instead, we talk about the number of ransomware, malware, or phishing attacks. Part of the reason for this is that the number of cyberattacks has grown so large that they don’t seem real.
Look at these statistics:
- cybercriminals breached 33 billion accounts in 2023
- 43% of all cyberattacks target small businesses
- 72.7% of organizations experienced a ransomware attack
- 93% of breaches start with phishing attacks, with 65% of those targeted spear phishing
- the average cost of cybercrime in the US is $27.27 million
And if you’d like a live view of cyberattacks, take a look at the FireEye Cyber Threat Map.
But the question remains – Why are there so many Cyberattacks?
MONEY IS THE BIGGEST MOTIVATOR
That’s right, based on 2023 stats, six out of every ten attacks extort money from companies and individuals – and that number is going up in 2024. The way the news reports cyberattacks, it might seem that big business is the most often targeted sector.
But that would be an incorrect assumption.
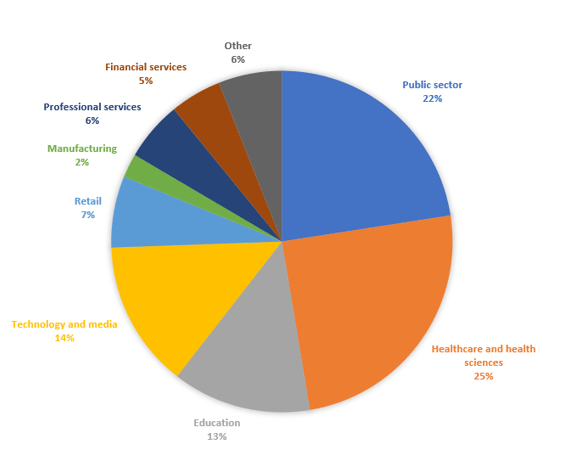
Healthcare – our medical records – suffer the most security incidents, followed closely by the Public – us. Together, these two sectors make up 47% of all security incidents. The reason for this is actually quite simple – most people don’t believe they are important enough to be targeted by cybercriminals.
This is yet another incorrect assumption because…
OUR DATA HAS VALUE
Do a Google search for a random product and then start paying attention to the ads that come up on the internet, and you will start seeing ads for those products.
Most of the information used to accomplish this is de-identified, meaning that while you see the advertisements, you are not specifically being targeted. Automated programs use the keywords you searched to target behaviors. In this way, anyone who searches for those keywords sees those ads.
DEFENDING AGAINST FILELESS MALWARE ATTACKS
Just as cybercriminals evolve their attacks, the cybersecurity industry learns how to defend against them. One of the most important ways to stop Fileless Attacks is to run software updates and perform regular maintenance. The most often breached systems are those that run older software or are missing security updates.
Unfortunately, the rise of this type of targeted advertising has put an unprecedentedly significant focus on consumer data. Today, every business in the world collects data on their customers to help them to better market their goods and services.
The problem is that businesses don’t de-identify the data they collect. They want to know where you live, how old you are, your gender, email address, phone number, what devices you use, etc. They can develop specific targeting algorithms for you and people like you by collecting this information. Cybercriminals realize this too, which is why they began attacking businesses and stealing this information.

OUR DATA IS MORE VALUABLE TO CYBERCRIMINALS
Cybersecurity experts track the number of breached records because that number directly relates to cyberattacks. This stolen personal data is collected and sold on the dark web for future attacks. In this way, cybercriminals are constantly feeding one another – they essentially have a black market for personal data, where everyone involved profits.

The Public sector – you and I – are under constant attack and we click on and average of 61% of phishing scams that hit our inboxes. Cybercriminals know we are going to fall for it, they have our data, and they use it to create phishing campaigns, spread malware, steal business credentials, plunder financial accounts, and so much more.
And this relates directly to the attacks on the Healthcare sector as it stores more personal information than any other entity. So by attacking this sector, they acquire the personal data sold to the cybercriminals who create the scams.
All this means that attacks on the Public sector – all of us – will continue to increase in number and complexity.
HOW DO I FIGHT BACK
Practice good cyber hygiene. Use Strong Passwords, enable 2-Factor Authentication, do Security Updates immediately, get a good AntiVirus, and Be Aware of the Cyber Threats out there. Cyberattacks aren’t going anywhere, so it’s up to all of us to protect ourselves.

Director of Cybersecurity and Marketing
I’ve always had a love of working with technology, being fortunate enough to have grown up with a grandfather who taught me how to fix things for myself and not be afraid to jump in and get my hands dirty. Over the last three decades, I’ve worked as a technician, trainer, technical writer, and manager in small businesses, enterprise organizations, and government. In addition, I’m an author, having published multiple works available online and in print. You can find my creative work at https://WritingDistracted.com
