When to Call for IT Support
Chuck's Cyber Wall
Social Engineering is not new. Criminals have been tricking people into revealing private or valuable information for millennia, but the methodology has evolved and developed dramatically over time. It is an art of deception, using the principles of human psychology to either build trust with someone or outright con them.
In the cyber world, this typically starts with inventing a plausible situation or story to obtain information, breach a system, or get money. Yes, you read that correctly. It starts with the scam, not the target.
But we’re getting ahead of ourselves. In order to defeat social engineering, we need to understand how it works and why it’s so effective. To do that, we will look at one of the best examples of social engineering from the movies.
WARGAMES
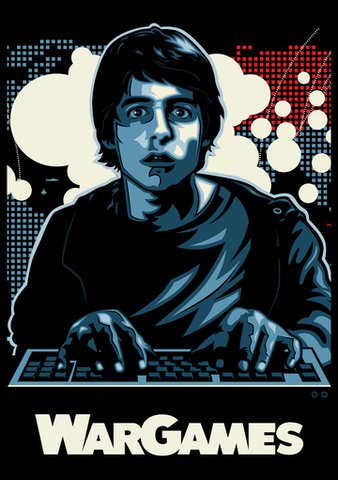
On June 3, 1983, we all watched a young hacker named David (Matthew Broderick) use his home computer to break into a secret government installation to play a game – and nearly started World War III. Although a fictional account and greatly simplified, there is some plausibility in the methodology of the hack, especially in discovering the backdoor password.
In the movie, David connects with an unidentified system with a list of games, one of which is Global Thermonuclear War. To access the game, he researches the developer, Stephen Falken, and discovers that Falken had a child named Joshua who died. Of course, Falken used his son’s name as the backdoor password, and discovering this information, David gained access to the games, allowing the plot to move forward.
That research into Falken is the essence of social engineering. Although portrayed innocently in the movie, David targeted the man, learned all about him by going to libraries to read books and news articles, and made the assumption that he used a password that was personal to him.
MODERN SOCIAL ENGINEERING
The world has come a long way since 1983. Now we have the internet and social media, making all that work to research individuals a whole lot easier. So easy, in fact, that targeting is no longer a requirement.
The first step of an attack is to create a generic scam and send it to as many people as possible. These scams most often take the form of phishing emails. Those who click on the malicious links and give up information about themselves become the targets – but it’s not usually the person who created the phishing scam that targets the individual.
While phishing scams gather information about people, the phishers sell that information on the dark web. Those cybercriminals who purchase the stolen data create more directed attacks, scraping additional information off social media sites or company web pages. In this way, they craft attacks that are methodically planned to manipulate their target into revealing information.
For example, finding pictures of a person working remotely lets the cybercriminal know that there might be security vulnerabilities to exploit. A picture of a particular model of laptop or phone might reveal software vulnerabilities. Celebrating a promotion or new job might tell the cybercriminal that the target has greater access levels. Posting about a particular product might give the cybercriminal a chance to create a fake ad that contains malware.
And let’s not forget all the information about friends and family members that you share or that’s shared about you.
We put so much exploitable information on the internet that we make the cybercriminal’s job easy.
DEFENDING AGAINST SOCIAL ENGINEERING ATTACKS
The best defense against social engineering is self-awareness. Cybercriminals construct attacks that prey on emotions, pretend to be friends and relatives, and make personalized offers that are simply too good to be true. They expect you to take action before considering the risks or picking up on the clues that tell you it’s a scam.
Beyond the ability to slow down and think before you click is the need to be proactive about your privacy and security. Among the proven most effective habits are:

- Never click on links in emails or messages
- Make sure you use Strong Passwords and a Password Manager
- Use 2FA (2-Factor Authentication) wherever possible
- Avoid sharing personal details on public social platforms
- Don’t use public WiFi without a VPN
- Keep all devices updated
- Check for known data breaches
When it comes down to it, protecting yourself against social engineering starts with education and awareness. We all enjoy sharing our successes and joys with our friends, but it comes with a risk. Think about it – no matter how safe you try to be online, you are only as secure as the least secure person in your circle.

Director of Cybersecurity and Marketing
I’ve always had a love of working with technology, being fortunate enough to have grown up with a grandfather who taught me how to fix things for myself and not be afraid to jump in and get my hands dirty. Over the last three decades, I’ve worked as a technician, trainer, technical writer, and manager in small businesses, enterprise organizations, and government. In addition, I’m an author, having published multiple works available online and in print. You can find my creative work at https://WritingDistracted.com
